Dating apps require users to disclose vulnerable information — and Yuna Ogura is Opened Up By A Train Thief Who Comes To Her House (2025)not just someone's romantic dreams. Most times, these apps require personal data like your name, age, and location. In the case of the latter, a new paper details that, for a time, several major apps left user locations able to be exposed by potential adversaries.
In a new paper out of Belgian university KU Leuven, "Swipe Left for Identity Theft," researchers break down potential privacy risks for 15 location-based dating apps (LBDs) with at least 10 million downloads. These days, dating apps are typically location-based in order to help users find matches physically close to them. By needing location, however, it opens users up to potential risks.
SEE ALSO: Daters are changing their app locations to the Olympic VillageAll apps except one used distance between users to measure location. (That exception, TanTan — an Asian dating app — used exact coordinates one-time at the point of matching, and only if they matched.) "However, lacking sufficient protections, the availability of distances can still lead to the inference of a user's location," the paper states. "This is done through trilateration."
Trilateration is the process of determining location by measuring distances between three triangles (or circles, or spheres). There are different types of trilateration apps use to determine location. The authors — Karel Dhondt, Victor Le Pochat, Yana Dimova, Wouter Joosen, and Stijn Volckaert — found that they were able to pinpoint almost an exact location in six out of 15 apps, as TechCrunch reported.
The most common vulnerability was through "oracle trilateration," which the paper explains, "Adversaries use an oraclethat indicates through a binary signal whether a victim is located within proximity, i.e., when they are within a defined 'proximity distance' from the attacker."
Hinge, Bumble, Badoo (which is owned by Bumble), and Hily were susceptible to such trilateration.
A Hinge spokesman told Mashable:
At Hinge, the safety and privacy of our users is always a top priority. Our app is built with a privacy-by-design approach and strictly protects sensitive user data. We are proud of our state-of-the-art bug bounty program and our ongoing dialogue with researchers, which are designed to attract comments so we can make adjustments before any harm happens to our users. We reviewed the feedback from this research team when we received it in early 2023 and immediately took action where appropriate.
A Bumble spokesperson told both TechCrunch and Mashable, "We were made aware of these findings in early 2023, and swiftly resolved the issues outlined. As a global business with members in countries all over the world, we are committed to protecting our users’ privacy and have adopted a global approach to privacy compliance."
This statement applies for Badoo as well, Bumble told Mashable.
Dmytro Kononov, CTO and co-founder of Hily, shared this statement with TechCrunch:
The findings indicated a potential possibility for trilateration. However, in practice, exploiting this for attacks was impossible. This is due to our internal mechanisms designed to protect against spammers and the logic of our search algorithm...Despite this, we engaged in extensive consultations with the authors of the report and collaboratively developed new geocoding algorithms to completely eliminate this type of attack. These new algorithms have been successfully implemented for over a year now.
Grindr was vulnerable to "exact distance trilateration." This can be done when services reveal exact distances to other users. The authors were able to figure out user locations as close as 111 meters (around 364 feet). Exact distance trilateration was possible even when the distance was hidden, such as in Egypt where Grindr hides all user locations for safety reasons.
SEE ALSO: Men found a surprising new way to lie on dating apps"The proximity Grindr offers to this community is paramount in providing the ability to interact with those closest to them, Grindr's chief privacy officer Kelly Peterson Miranda told TechCrunch. "As is the case with many location-based social networks and dating apps, Grindr requires certain location information in order to connect its users with those nearby...Grindr users are in control of what location information they provide."
Finally, the app happn was vulnerable to "rounded distance trilateration," which can be done if an app utilizes a rounded location as a precaution. CEO and president of happn, Karima Ben Abdelmalek, told TechCrunch:
After review by our Chief Security Officer of the research findings, we had the opportunity to discuss the trilateration method with the researchers. However, happn has an additional layer of protection beyond just rounding distances...This additional protection was not taken into account in their analysis and we mutually agreed that this extra measure on happn makes the trilateration technique ineffective.
It appears that for apps with these vulnerabilities, the apps took measures to stop bad actors from determining user location using trilateration, with the exception of Grindr.
According to the paper, Tinder and LOVOO used "grid snapping" to prevent trilateration. Grid snapping is a technique of dividing one's location into a grid of squares. Coordinates (aka where users are) are moved to the center of these squares (Tinder) or the right side (LOVOO) and one's distance is measured from there. Therefore, their actual distance is inaccurate and can't be trilaterated.
Plenty of Fish and Meetic don't access GPS locations. While MeetMe, Tagged, and OkCupid do access this information, they convert it to the nearest town. The authors couldn't reverse engineer the information they needed for TanTan and Jaumo, so they couldn't test this method to find user locations.
The paper shows the importance of caution when using dating apps. As the paper concludes, "We hope that the awareness that we bring of these issues will lead LBD app providers to reconsider their data gathering practices, protect their APIs [application programming interfaces]from data leaks, prevent location inference, and give users control of their data and therefore ultimately their privacy."
Topics Apps & Software Privacy
 Episode 4: The Wave of the Future
Episode 4: The Wave of the Future
 Zora Neale Hurston on Zombies by Sadie Stein
Zora Neale Hurston on Zombies by Sadie Stein
 Lost Ferraris, and Other News by Sadie Stein
Lost Ferraris, and Other News by Sadie Stein
 Conspiracy Theories, and Other News by Sadie Stein
Conspiracy Theories, and Other News by Sadie Stein
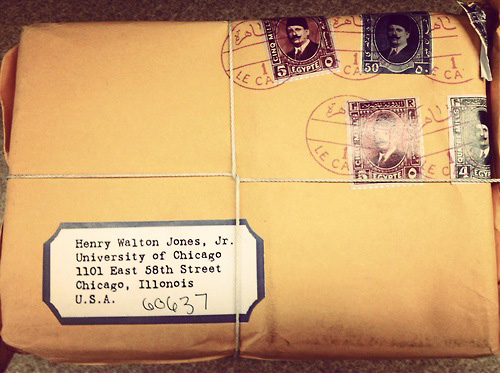 How to Get into College, Indiana Jones Edition by Sadie Stein
How to Get into College, Indiana Jones Edition by Sadie Stein
 GoT Beer, and Other News by Sadie Stein
GoT Beer, and Other News by Sadie Stein
 Happy Birthday, Huck! by Sadie Stein
Happy Birthday, Huck! by Sadie Stein
 How to Settle Down with Dystopia
How to Settle Down with Dystopia
 Bookless Libraries, and Other News by Sadie Stein
Bookless Libraries, and Other News by Sadie Stein
 Sony launches new flagship XM6 headphones: Order them now
Sony launches new flagship XM6 headphones: Order them now
 Things Behind the Sun by Brian Cullman
Things Behind the Sun by Brian Cullman
 The Hatchet Falls by Sadie Stein
The Hatchet Falls by Sadie Stein
 The Perfect Stocking Stuffer by Sadie Stein
The Perfect Stocking Stuffer by Sadie Stein
 NYT Strands hints, answers for May 5
NYT Strands hints, answers for May 5
 David Opdyke by Yevgeniya Traps
David Opdyke by Yevgeniya Traps
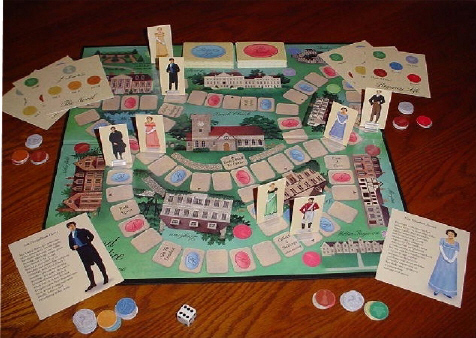 A Truth Universally Acknowledged by Sadie Stein
A Truth Universally Acknowledged by Sadie Stein
 Lists of Lists, and Other News by Sadie Stein
Lists of Lists, and Other News by Sadie Stein
 Episode 4: The Wave of the Future
Episode 4: The Wave of the Future
 Conspiracy Theories, and Other News by Sadie Stein
Conspiracy Theories, and Other News by Sadie Stein
Documenting the DooOn the Pleasures of Not ReadingThe Guilt of Unsubscribing from NewslettersThe Last Bastion of Print: The TheatreChina Has Ripped Off Anish Kapoor’s “Bean” SculptureDocumenting the DooHunter S. Thompson Rides with the Hells AngelsIn Which Hayden Carruth Complains About a Holiday InnDesign a Cover for the 20th Anniversary of Infinite JestNext Tuesday: James Salter’s Memorial ServiceStaff Picks: Buses, Basements, Boots, BedThe Last Bastion of Print: The TheatreFrom the Archive: “Mannerism,” a Poem by René RicardNext Tuesday: James Salter’s Memorial ServiceThe Wedding of the Painted DollOn the Pleasures of Not ReadingWhen You Marry Someone Who Has the Same Last NameA Love Letter from Guillaume Apollinaire, in the TrenchesBeautiful Image, or, Adolescence at the SpaLeslie Jamison and Ryan Spencer Take on the Apocalypse Letter from Portugal: Sonnets from the Portuguese by Sadie Stein Fuzzy Austen, Tipsy Wilde by Sadie Stein The “American Idol of Microfiction” Gets a New First Prize by The Paris Review Man Pulls Sword over Badly Treated Book: Happy Monday! by Sadie Stein 112 Greene Street by Claire Barliant John Jeremiah Sullivan Answers Your Questions by John Jeremiah Sullivan In Memory of Daryl Hine by Sadie Stein Helpmeets, Field Guides, Burning Questions by Sadie Stein How Is the Critic Free? by Caleb Crain Stage Struck by Scott Korb Buy Elvis’s Library Card by Sadie Stein Wharton, Borges, and Grey: Fan Dr. Collier by Julian Tepper What We’re Loving: Dorian Gray, Sex with Immortals by The Paris Review On Press with The Paris Review by Stephen Hiltner The Finalists: Win a Bicycle Contest by The Paris Review The Dead Preside by Brian Gittis My Little Pony, Typography Humor by Sadie Stein David Rakoff, 1964–2012 by Lorin Stein In Which the Author Reads the Works of Albert Cossery: An Illustrated Essay by Nathan Gelgud
2.5424s , 10153.890625 kb
Copyright © 2025 Powered by 【Yuna Ogura is Opened Up By A Train Thief Who Comes To Her House (2025)】,Pursuit Information Network